Our Products
adam:ONE® Zero Trust Connectivity (ZTc) with DNSharmony® intelligence aggregation - protecting any device, anywhere
adam:ONE®
The world's first Zero Trust resolver - featuring Muscle-Brain architecture for Default-Deny-All networking that actually works in production.
Don't Talk To Strangers (DTTS)®
Patented technology that denies all IP connections by default unless first requested by DNS and allowed by policy
Muscle-Brain Hybrid
Distributed deployment for performance and resilience, with centralized single-pane-of-glass control
Device-Agnostic Protection
Out-of-band protection works with any device - no endpoint agent required
AI-Driven Dynamic Allowlisting
Intelligent policy creation with decisive answers to first-time queries 20 times faster than the blink of an eye
Full Layer 2 Visibility
Complete network visibility with automatic device discovery and quarantine
DNSharmony®
pDNS intelligence aggregation that combines multiple pDNS resolvers for enhanced threat detection and resilience.
Resilient by Design
Redundant pDNS resolution ensures uptime even if upstream resolvers fail
Optimized Performance
Parallel DNS queries deliver faster response times and reduced latency
Continuous Domain Validation
Acts as resolver of last resort - continuously validates that previously trusted domains have not turned malicious
Enterprise-Wide Visibility
Centralized logging and analytics across all pDNS resolver activity for compliance and threat investigation
Enhanced Preemptive Security
Aggregate any pDNS resolvers of your own choice to get the composite world's best intelligence feeds in real time
Multi-Source Threat Intelligence
Aggregates multiple competing pDNS resolvers that do not share intelligence, giving defenders access to unique threat feeds that cannot normally be combined
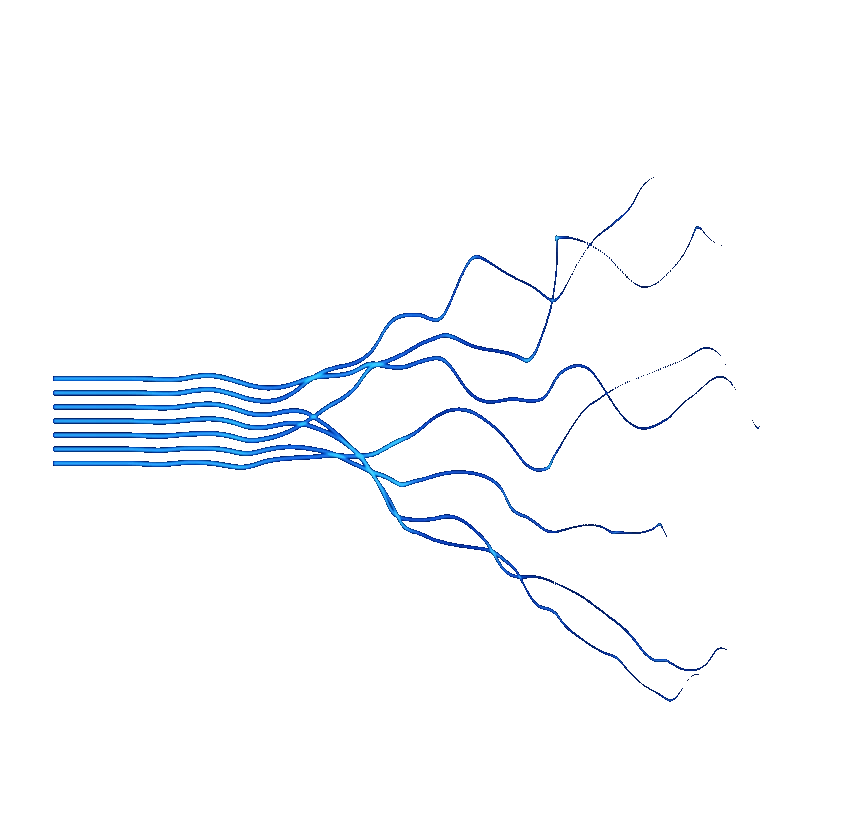
The Protection Flow
How adam:ONE® + DNSharmony® Work Together
Multi-layered Zero Trust protection combining pDNS threat intelligence aggregation with Default-Deny-All network security
Default-Deny-All
Start in a Default-Deny-All state. AI-driven dynamic allowlisting writes policy as a device needs to access verified connections.
DNS as Root of Trust
Enforces a ZT DNS element via patented DTTS® technology - denying all IP connections unless first requested by DNS and allowed by policy.
Verify and Connect
Opens a hole for the verified connection, then collapses it as soon as the connection expires. Zero lingering attack surface.
DNSharmony® Cross-Check
Allowed connections are cross-checked by aggregated pDNS resolvers of your choice for real-time threat intelligence and resilience.
This same Zero Trust protection extends beyond the enterprise
adam:GO®
Zero Trust Connectivity protection for mobile and multi-homed devices. Extend the same Default-Deny-All security from adam:ONE® to every device, everywhere - regardless of network.
Protection On the Go
Full DTTS® and Zero Trust enforcement on any device, on any network - office, home, or public Wi-Fi
Cross-Platform Support
Available for Windows, iOS, iPadOS, Mac OS, Chrome OS, and Android
Unified Policy Management
Managed through the same adam:ONE® dashboard - one policy engine for your entire organization
Circumvention-Proof
Unauthorized DoH, DoT, and Proxies are denied by default - preventing bypass attempts
Proven Against Advanced Threats
Demonstrated immunity to Pegasus Forced Entry* and other APTs through ZTc connectivity - achieved before the threat became known
adam:APN™
Extend adam:ONE® Default-Deny-All protection to cellular-connected devices through a custom Access Point Name - bringing Zero Trust to any cellular endpoint.
Cellular Zero Trust
Delivers adam:ONE® services directly through a custom APN - no device agent required for cellular protection
Same Default-Deny-All Protection
Cellular devices receive the same DTTS® enforcement as enterprise network devices
Carrier Integration
Works with carriers that offer custom APN options - provisioned via SIM/eSIM or MDM
Transparent to the User
Protection is applied at the network level - no apps to install, no settings to configure on the device
Device-Agnostic OT/IoT Protection
Secures operational technology and IoT devices in the field that cannot run a software agent - protection is delivered at the network layer